Mastering RemoteIoT Device SSH: The Ultimate Guide For Secure Connectivity
Are you ready to dive into the world of RemoteIoT device SSH? If you're here, chances are you're either a tech enthusiast or someone looking to secure their IoT setup. RemoteIoT device SSH is more than just a buzzword; it's a game-changer for anyone dealing with Internet of Things (IoT) devices. Whether you're a beginner or a seasoned pro, this guide will walk you through everything you need to know about securely connecting and managing your IoT devices remotely.
Let's face it, IoT devices are everywhere these days. From smart homes to industrial automation, they're revolutionizing how we interact with technology. But with great power comes great responsibility, and that's where RemoteIoT device SSH comes in. Think of it as the digital lock that keeps your devices safe from prying eyes while still letting you access them from anywhere in the world.
Now, before we get too deep into the nitty-gritty, let's clear something up. This isn't just another tech article filled with jargon that makes your head spin. We're keeping it real, breaking things down step by step, so even if you're new to the game, you'll walk away with actionable knowledge. So, buckle up because we're about to take this RemoteIoT device SSH journey together!
Read also:Unpacking The Power Of Ljisd Clever Your Ultimate Guide
Understanding RemoteIoT Device SSH
What Exactly is SSH?
SSH, or Secure Shell, is like the secret handshake of the tech world. It's a protocol that lets you securely connect to remote devices over a network. When we talk about RemoteIoT device SSH, we're referring to using this protocol specifically for IoT devices. Imagine being able to control your smart thermostat from the other side of the planet without worrying about hackers sneaking in—that's the power of SSH.
Here's the deal: SSH encrypts all your communication, making it nearly impossible for anyone to intercept your data. It's like having a private conversation in a crowded room where no one else can hear what you're saying. For IoT devices, this level of security is non-negotiable, especially when they're handling sensitive information.
Why RemoteIoT Device SSH Matters
IoT devices are awesome, but they're also vulnerable. Without proper security measures, they can become easy targets for cyberattacks. That's where RemoteIoT device SSH shines. By implementing SSH, you're adding a robust layer of protection that keeps your devices safe from unauthorized access.
Let me break it down for you:
- SSH ensures secure communication between your device and the network.
- It authenticates users, so only authorized individuals can access the device.
- It encrypts all data transfers, keeping your information private.
And let's not forget, with more and more devices connecting to the internet every day, the need for secure remote access is only going to grow. RemoteIoT device SSH is not just a trend; it's a necessity.
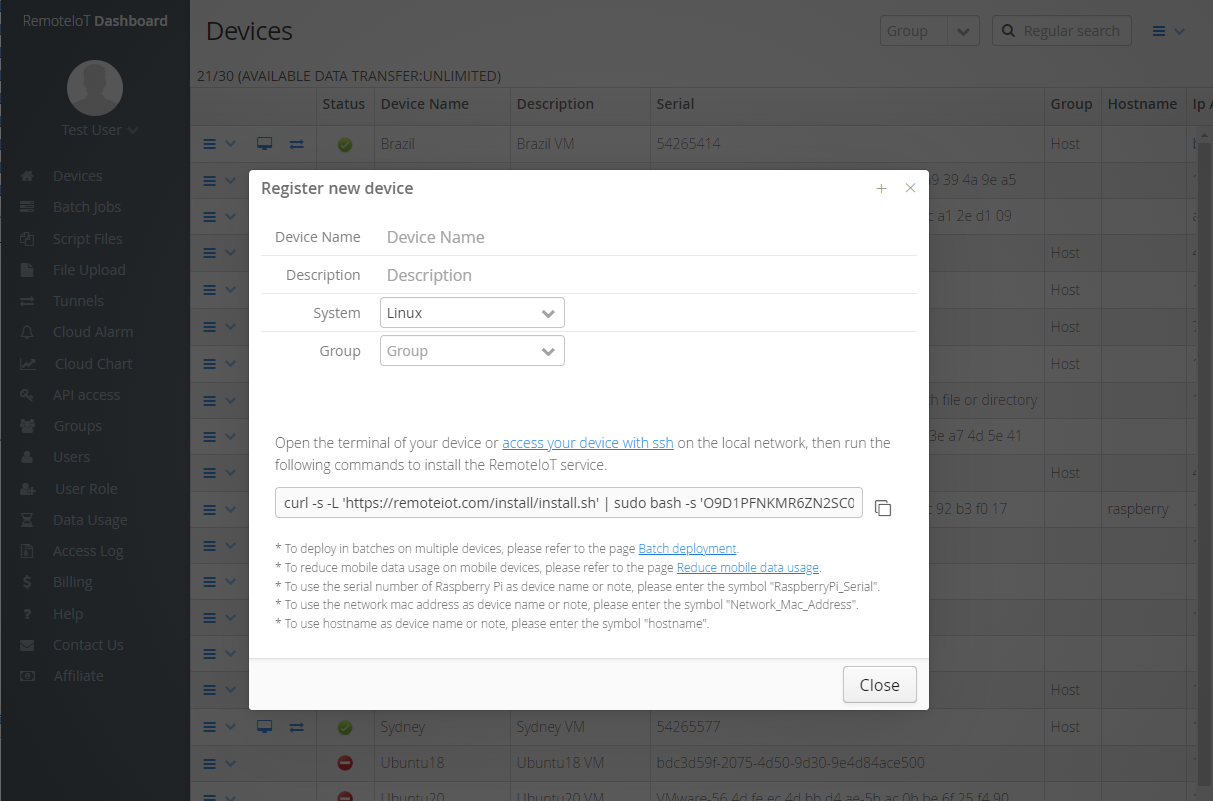
Setting Up RemoteIoT Device SSH
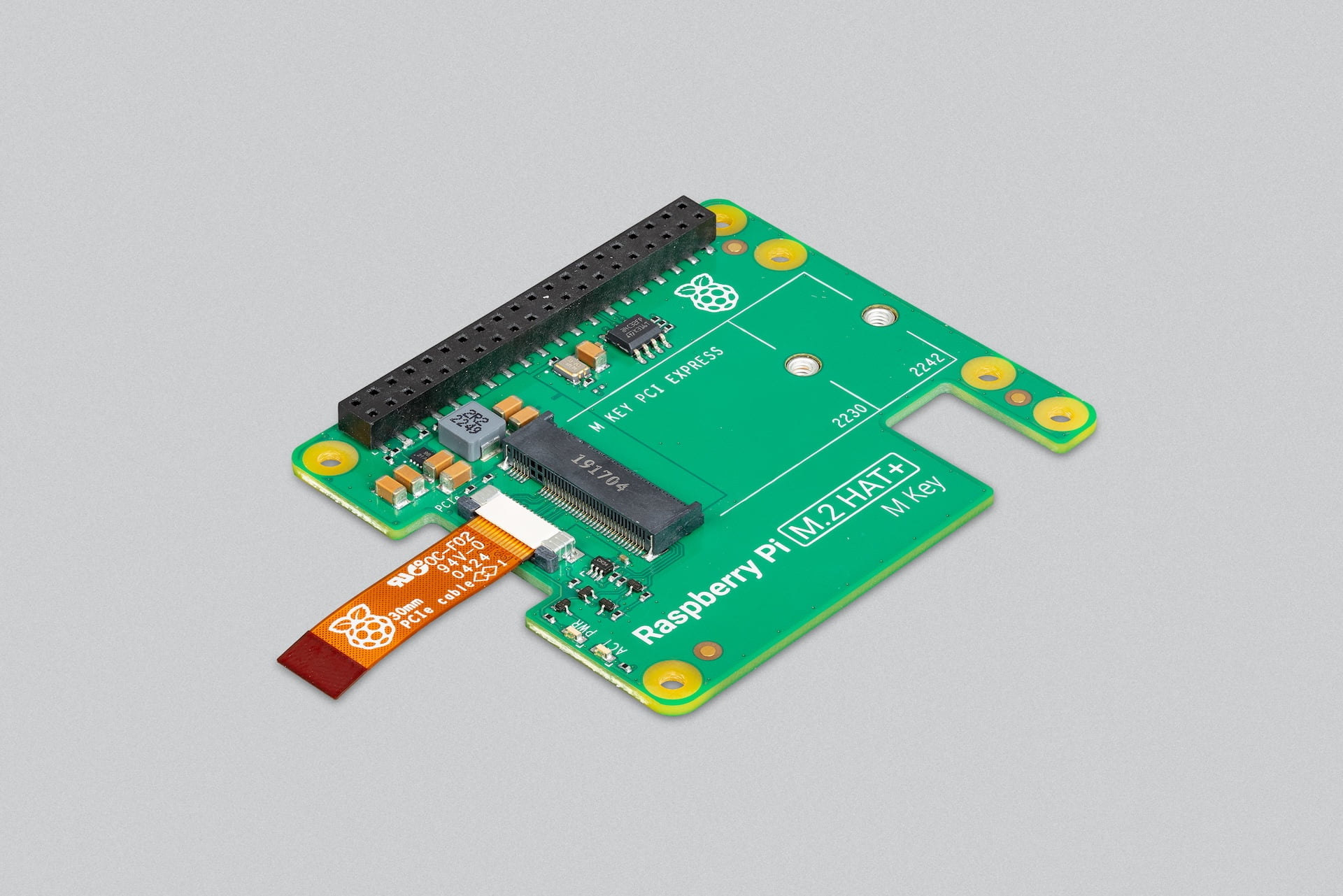
Step 1: Preparing Your IoT Device
Before you can SSH into your IoT device, you need to make sure it's ready for the connection. This usually involves enabling SSH on the device itself. Most modern IoT devices come with SSH pre-installed, but you'll still need to activate it.
Read also:Carlos Klove Wife The Untold Story Of Love Fame And Family
Here's a quick checklist to get you started:
- Check if SSH is already enabled on your device.
- If not, refer to your device's manual for instructions on enabling SSH.
- Make sure your device is connected to the internet.
Once your device is prepped and ready, you're one step closer to secure remote access.
Step 2: Generating SSH Keys
SSH keys are like digital passports that allow you to access your IoT device without needing a password every time. Generating these keys is a crucial step in setting up RemoteIoT device SSH.
Here's how you do it:
- Open your terminal or command prompt.
- Type in "ssh-keygen" and hit enter.
- Follow the prompts to create your public and private keys.
These keys will be your ticket to accessing your device securely. Just remember, your private key is like a master key—don't share it with anyone!
Best Practices for RemoteIoT Device SSH
Use Strong Passwords
Even though SSH keys provide an extra layer of security, it's still a good idea to use strong passwords. Think of it like having a deadbolt on your front door. The more secure your password, the harder it is for intruders to break in.
Here are some tips for creating strong passwords:
- Use a mix of uppercase and lowercase letters.
- Include numbers and special characters.
- Avoid using easily guessable information like birthdays or pet names.
And don't forget, change your passwords regularly to keep things fresh.
Regularly Update Your Device
Just like how you update your phone or computer, it's important to keep your IoT devices up to date. Software updates often include security patches that fix vulnerabilities. By staying current, you're reducing the risk of your device being compromised.
Here's a simple way to remember:
- Set reminders to check for updates.
- Install updates as soon as they're available.
- Restart your device after updating to ensure everything runs smoothly.
Updating might seem like a hassle, but trust me, it's worth it in the long run.
Common Challenges with RemoteIoT Device SSH
Firewall Issues
Firewalls are great for protecting your network, but they can sometimes block SSH connections. If you're having trouble connecting to your IoT device, chances are your firewall is the culprit.
Here's how you can fix it:
- Check your firewall settings to see if SSH is allowed.
- Open the necessary ports for SSH (usually port 22).
- Make sure your device's IP address is whitelisted.
By tweaking your firewall settings, you can ensure smooth SSH connections without compromising your network's security.
Network Connectivity Problems
Even with everything set up correctly, network issues can still prevent you from accessing your IoT device via SSH. Poor internet connection or router problems can disrupt your connection.
Here's what you can do:
- Restart your router to refresh the connection.
- Check your internet speed to ensure it's sufficient for SSH.
- Consider using a wired connection if Wi-Fi is unstable.
Stable network connectivity is key to maintaining a reliable SSH connection.
Advanced Features of RemoteIoT Device SSH
Port Forwarding
Port forwarding is like creating a direct line to your IoT device from the outside world. It allows you to access your device remotely without needing to be on the same network.
Here's how it works:
- Log in to your router's admin interface.
- Find the port forwarding settings.
- Set up a rule to forward port 22 to your IoT device's IP address.
With port forwarding, you can SSH into your device from anywhere, as long as you have the internet.
SSH Tunneling
SSH tunneling is a powerful feature that lets you securely transfer data between your device and a remote server. It's like creating a private tunnel that only you can use.
Here's why you should consider using SSH tunneling:
- It adds an extra layer of security to your data transfers.
- You can use it to bypass firewalls or restricted networks.
- It's perfect for sensitive operations that require privacy.
SSH tunneling might sound complex, but once you get the hang of it, it's a game-changer for secure remote access.
Security Tips for RemoteIoT Device SSH
Enable Two-Factor Authentication
Two-factor authentication (2FA) is like having a second lock on your door. Even if someone manages to get your password, they still need the second factor to gain access.
Here's how to set it up:
- Install a 2FA app on your phone.
- Configure your IoT device to use 2FA.
- Follow the prompts to link your device with the app.
With 2FA enabled, you're adding an extra layer of protection that makes unauthorized access much harder.
Monitor Your Connections
Keeping an eye on who's accessing your IoT device is crucial for maintaining security. Regularly checking your connection logs can help you spot any suspicious activity.
Here's what you should do:
- Set up logging for SSH connections.
- Review the logs periodically for any unusual activity.
- Block any IP addresses that attempt unauthorized access.
By staying vigilant, you can quickly address any potential security threats.
Future Trends in RemoteIoT Device SSH
Quantum Computing and SSH
As technology advances, so do the methods of securing our devices. Quantum computing is on the horizon, and it could potentially break traditional encryption methods. That's why researchers are already working on quantum-resistant algorithms for SSH.
Here's what you need to know:
- Quantum-resistant algorithms are designed to withstand attacks from quantum computers.
- They're still in the experimental stage but show promising results.
- As they become more mainstream, they'll revolutionize how we approach SSH security.
Staying ahead of the curve is essential in the ever-evolving world of cybersecurity.
AI and Machine Learning in SSH
Artificial intelligence and machine learning are also making their way into SSH. These technologies can analyze patterns and detect anomalies that might indicate a security breach.
Here's how they're changing the game:
- AI can predict potential threats before they happen.
- Machine learning algorithms can adapt to new attack vectors.
- They provide real-time insights that help strengthen your security posture.
Embracing these advancements will keep your RemoteIoT device SSH setup future-proof.
Conclusion
And there you have it, folks! We've covered everything from the basics of RemoteIoT device SSH to advanced features and future trends. By now, you should have a solid understanding of how to securely connect and manage your IoT devices remotely.
Remember, security is a journey, not a destination. Stay informed, keep your devices updated, and always be on the lookout for new threats. If you found this guide helpful, don't forget to share it with your friends and colleagues. And if you have any questions or comments, feel free to drop them below. Let's keep the conversation going and make the IoT world a safer place, one SSH connection at a time!
Table of Contents:
Article Recommendations